Sentinel One

The First Cyber Security AI Platform to Protect the Entire Enterprise.
Break down security silos. Gain enterprise-wide visibility and control. Action your data in real time with AI
In the battle against ever-evolving cyber threats, we need to act faster and smarter than what’s possible with human-powered technology. SentinelOne is autonomous cybersecurity built for what’s next.
Sautech is a Authorized Partner of SentinelOne. We offer Cloud Managed Solution on Sentinelone so you are always monitored. This is a must have enterprise Cyber Security Software for devices.
Starting from : R150 per Month.
CheckPoint Firewall

CheckPoint Firewall Integrating the most advanced threat prevention and consolidated management, our security gateways are designed to prevent any cyber attack, reduce complexity and lower your costs.
Check Point firewall software utilizes multiple technologies to inspect for the port, source, and destination rules, and also for application-level vulnerabilities. Using separate modules for the scans (e.g., Web, abnormal activity, and DoS), Firewall1 provides high throughput.
We offer dedicated hosting in three forms namely:
- Device Support
- Licensing
- Managed Services and Outsourced Support
- The Above can be branch devices or hosted dacentres instances
Starting from: R1500 per instance per month.
Server and Infrastructure Optimization
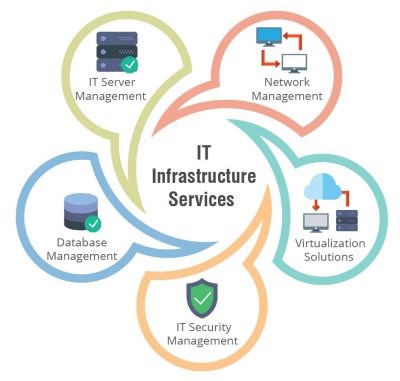
Server and infrastructure optimization is a crucial aspect of maintaining an efficient and high-performing IT environment. It involves the systematic enhancement of server hardware, software, and overall network infrastructure to maximize resource utilization, improve response times, and minimize downtime. By deploying various optimization techniques such as load balancing, virtualization, and efficient storage solutions, organizations can ensure that their servers operate at peak efficiency while accommodating growing workloads. This process not only enhances system reliability but also contributes to cost savings through better energy utilization and reduced hardware requirements. Continuous monitoring and analysis of server performance are essential components of optimization, allowing for proactive adjustments to ensure that the IT infrastructure aligns with evolving business needs. Ultimately, server and infrastructure optimization plays a pivotal role in enhancing overall system resilience, scalability, and the ability to adapt to the dynamic demands of modern computing environments.
Sautech specializes in Maintaining Servers including Windows and Linux environments, Pastel and SQL implementations. Our Team performs Maintenance Services, Adhoc SLA Onsite and Remote Support.
Our Team focuses on a mananged backup solution together with our Site24 Monitored services we are always one step ahead.
Starting from R250 per support request.
Penetration Testing

Penetration testing, often referred to as ethical hacking, is a proactive cybersecurity practice designed to assess the vulnerability of a system, network, or application. Skilled professionals, known as penetration testers or ethical hackers, simulate real-world cyberattacks to identify weaknesses that malicious actors could exploit. The goal is to uncover security flaws before they can be utilized by attackers, enabling organizations to strengthen their defenses. Penetration testing involves a systematic and controlled approach, which may include reconnaissance, vulnerability analysis, exploitation, and post-exploitation analysis. By conducting penetration tests, businesses can gain insights into potential security risks, prioritize remediation efforts, and ultimately fortify their cybersecurity posture, ensuring the confidentiality, integrity, and availability of their digital assets. Regular and thorough penetration testing is a crucial element of a comprehensive cybersecurity strategy in today’s constantly evolving threat landscape.
Penetration-Testing-in-Cyber-Security
Sautech has performed multiple Cyber Security Penetration Testing throughout Southern Africa.
Our Team uses multiple technologies and our reports are often used by Insurance companies and IT Providers to assist their clients.
We offer a no-nonsense approach with our Certified Engineers to provide usefull information together with a “how to” guide in implementing our findings and recommendations to further secure your environment.
Starting from R5000 per IP device.
ETHICAL HACKING (white hat)
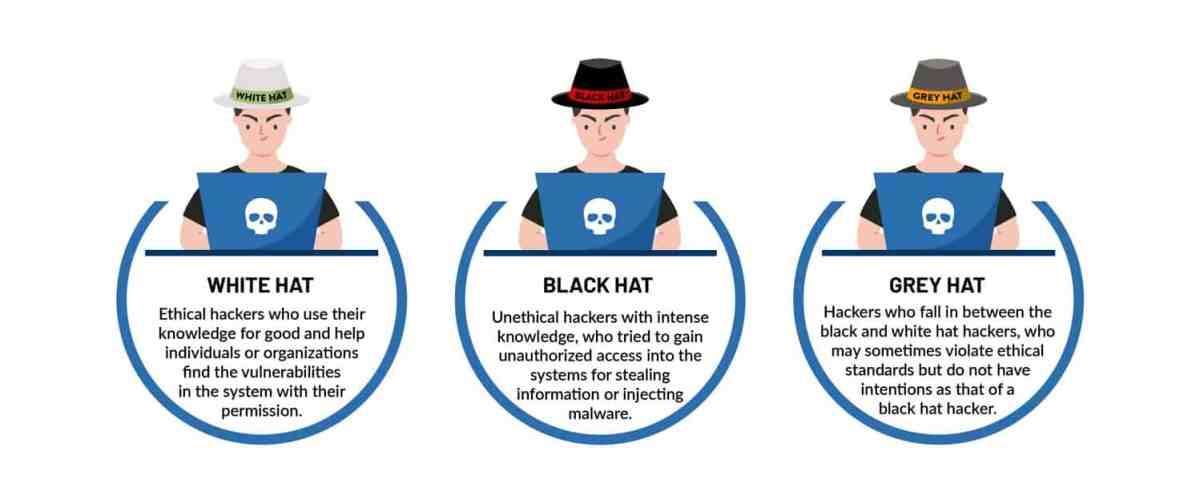
The goal of Ethical Hacking is to simulate real-world cyber threats and help organizations strengthen their defenses against potential cyberattacks. Ethical hackers employ various techniques and tools to mimic the tactics of malicious actors, providing valuable insights into a system’s vulnerabilities. By identifying and addressing these weaknesses proactively, ethical hacking plays a crucial role in enhancing overall cybersecurity, ensuring the integrity and security of digital assets while helping organizations stay one step ahead of potential cyber threats.
We focus on:
- Vulnerability Assessment: Ethical hackers conduct thorough assessments of systems to identify potential vulnerabilities. This involves using various tools and techniques to analyze software, network configurations, and infrastructure components.
- Penetration Testing: Ethical hackers perform controlled simulated attacks, known as penetration tests, to exploit identified vulnerabilities. This process helps organizations understand how their systems might be compromised and allows them to address weaknesses before malicious hackers can exploit them.
- Security Auditing: Ethical hackers conduct comprehensive security audits to review and assess an organization’s overall security posture. This involves examining policies, procedures, and configurations to ensure they align with industry best practices and compliance standards.
- Social Engineering Testing: Ethical hackers often employ social engineering techniques to test the human element of security. This includes attempting to manipulate individuals within the organization to gain access or extract sensitive information, helping to uncover potential weaknesses in employee awareness and training.
- Security Patching and Remediation: Ethical hackers collaborate with organizations to develop and implement strategies for patching and remediation. After identifying vulnerabilities, they work with the IT and security teams to prioritize and address issues, ensuring that the necessary security patches and measures are applied to mitigate risks.